Over the last week the news has been littered with stories about data leaks. From one of the biggest data leaks in history, the Panama Papers* to a movie that tells the story about a data leak a long time ago, in a galaxy far far away! “Rogue One” coming out in late 2016. Star Wars fans finally get to see the first canonical storyline regarding how the plans for the original Death Star were stolen by the rebels.
With these two stories catching the headlines, I felt like putting together a quick last-minute work of fan fiction combining the Star Wars universe with threats that exist in our world and have been loosely connected to massive data leaks.
How the rebels might have gotten the Death Star plans if the empire was running insecure website software.
It is not far fetched to assume the Empire is built on bureaucracy. It likely included multiple layers of strict policies and paperwork to fill out for the various departments as they request assets, such as websites or, more accurate, blasters. Somewhere in this mix imagine a department of propaganda is tasked with running something like a website and, for the sake of simplicity, they’d choose software similar to WordPress to help them distribute the emperor’s pro-Empire message easily and efficiently to readers galaxy wide. The Empire’s IT team sets up the server as the propaganda department requested on the Empire’s internal servers, because they have plenty of resources like servers and data center space for all the Empire’s IT needs they are smart and set it up on their own system separate from systems that handle email or collect invoices from Blacksun. Like any good website owners, the propaganda team customized the site with plugins/themes and, of course, set up accounts for both the Emperor and Vader so they have direct access to write posts about the future plight of the Bothans and such.
With the above scenario, the site would likely get plenty of funding and attention when it was first set up. Vader would be writing his monthly state of the empire addresses and the Emperor occasionally write posts like “The top 10 things that make a Sith better than a Jedi”. Everything runs smoothly for a few years and eventually the people who set up the site and handled updates get promotions to new departments. The people who still log in to the site choose to ignore those “update available” warnings because “someone else had always taken care of those.”
Then came one fateful day, which passed like any other day … The “updates available” notices still being ignored and security patches being missed. One unnamed rebel tries an exploit and is amazed that the site that has gone unnoticed is now in their control. Being smart, they don’t modify any content on the site itself (although the idea of writing a post by Vader about how the Emperor never washes his robe would have been epic) they instead see what data they can pull off the site. They have access to the site’s files, databases and little else (remember, the IT team for the empire only built this server for the purpose of just this site) … But, the rebels now had access to the hashed passwords in the database and a place to run commands and access other systems from within the Empire’s network.
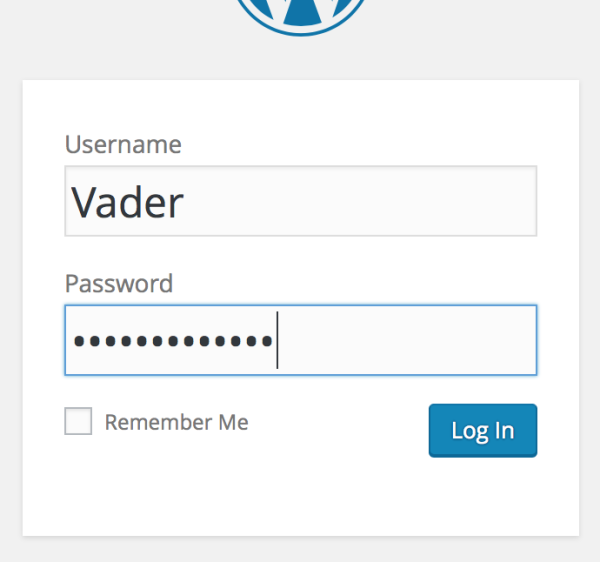 They get to cracking the passwords: The Emperor’s password of “123456” is guessed immediately, Vader’s password gets figured out some time later: being “Vader<3sPadme” it had more complexity.
They get to cracking the passwords: The Emperor’s password of “123456” is guessed immediately, Vader’s password gets figured out some time later: being “Vader<3sPadme” it had more complexity.
With their new knowledge, the rebel’s turn their attention to attempting to do what any self-respecting rebel hacker would, pivot and gain further access. They use what information they have now, Vader’s and the Emperor’s email addresses which are part of the account, and their passwords, plus access from a system that happens to be inside the Empire’s internal or “secure” network.
The Emperor’s password doesn’t work on palpatine@the.empire, but they get a lucky break with vader@the.empire’s password matching and they get access to a treasure trove of internal documents. Including an email with the subject line “RE: Death Star plans for your review” he was CC’d on, with an attachment of some value to the rebels.
Next thing you know, the plans are in the hands of the rebels and being sent to a ship in service of the House of Organa. Vader, feeling ashamed of being at fault takes an Imperial I-class Star Destroyer named Devastator to square off with the much smaller Corellian corvette just outside the orbit of a small desert planet named Tatooine.
There you have it, my little WordPress+Star Wars security fanfic. Now, of course, this is all conjecture and you’ll have to wait for the release of “Rogue One” later this year to find out the truth. Of course, if it turns out to contain any spoilers I will apologize and promise I did not have a bootleg copy of the movie or script.
We’ve seen plenty of data leaks in real life, though, and even the biggest empires, smallest corporations and personal blogs benefit from the moral of the above story:
- keep websites for non-critical needs separate from the private or corporate network
- have it be managed by teams of security professionals that will maintain (update) the systems
- never share/reuse passwords.
Farewell, and may the force be with you.
