The word “disaster” is one you never want to hear in business. Even if it’s a seemingly minor disaster, it usually means taking time away from business to investigate the root cause, clean up the mess, update processes, and sometimes even apologize to clients or employees who were harmed in the wake of it.
But it’s not just business operations or physical workspaces affected by disaster. WordPress websites can face their own kinds of disasters.
WordPress security breaches are definitely the most common.
User error can also play a role in the (unintentional) harm of a WordPress site.
Natural disasters can contribute their own kind of destruction if they reach the main location of your web server.
Even WordPress itself can lead to disaster if your website isn’t managed properly and securely. This is most commonly seen with cowboy coding or the issuing of plugin or theme updates on a live site without first testing them in a safe staging environment.
Not to sound completely pessimistic, but disaster is all around us. And, even though we can mitigate for known risks, something bad could still happen down the road. It might be an easy enough issue to fix, but any downtime, defacement, or broken functionality on the frontend of your website is bad.
A disaster recovery plan will help you prepare, prevent, and handle one if and when it does happen.
The Costs of a Disaster in WordPress
An IBM-sponsored report, the 2017 Cost of Data Breach Study, provided some revealing facts about the state of web security and how expensive cleanup can be in the face of a breach. Although this report focuses mostly on data breaches, I want to remind you that anything that affects the “face” of your online brand can be harmful and costly to your business.
So, let’s focus on the overall message of this report — that disaster can affect any website and will lead to serious consequences if left unchecked-— and make our way from there. Here are the key takeaways:
Cost of Data Breaches and Other Disasters
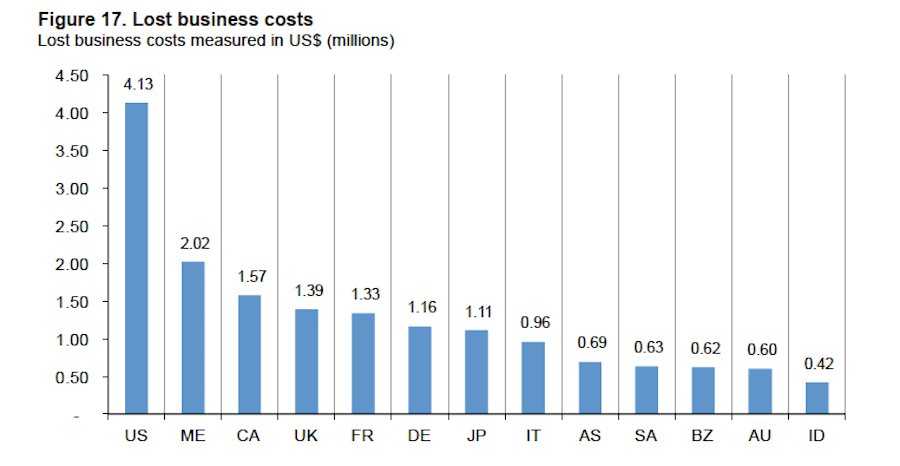
As you can see from this chart, North American countries are the ones currently faced with the most expensive data breaches.
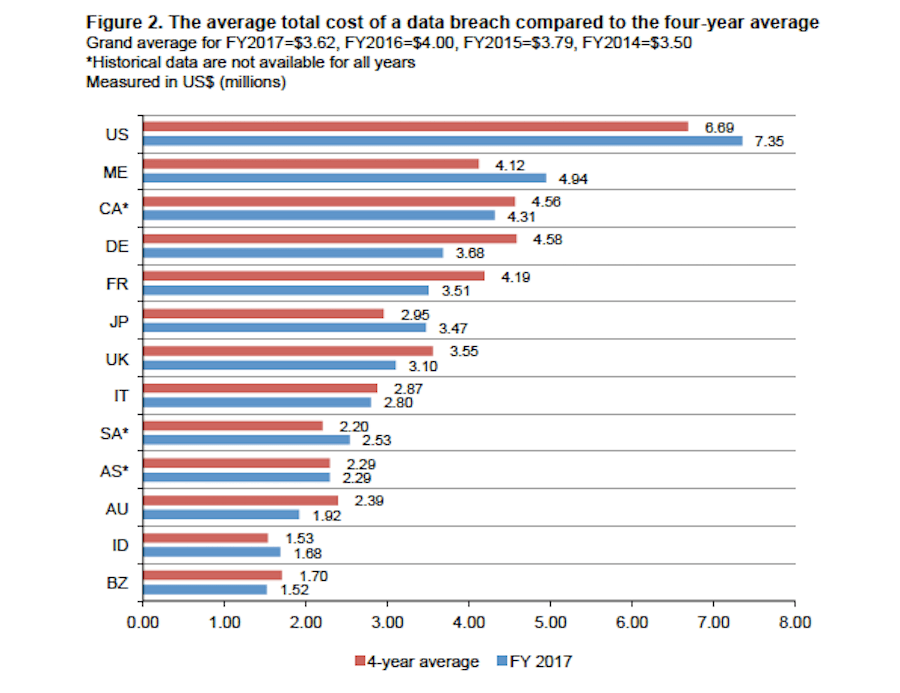
On average, the cost of a data breach amounts to $3.62 million.
Now, if we want to break that down by person (and corresponding records stolen), it’s best if we look at the industry distribution of costs per capita:
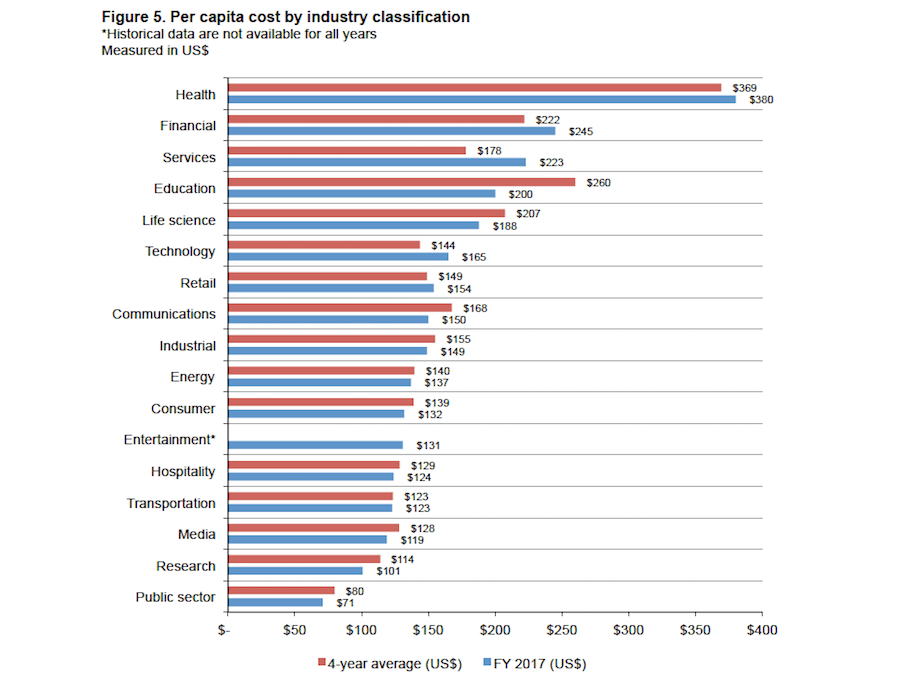
For those of you working in the health, financial, and education sectors, you can see how expensive every stolen record can be. That’s, of course, not to discount the costs to other industries as the average cost per stolen or lost record is $141. Multiply that by however many records your website holds and you can imagine what that sort of hit your profit would take as a result.
The same sort of logic applies to anything that forces your WordPress site to stop working or to go offline altogether. The cost of downtime can be calculated by:
- Starting with the amount of revenue your site earns in an hour.
- Multiplying it by the amount of hours your site was offline.
- Adding the costs of running a website per hour.
- Adding the costs of website recovery activities, including the time you or your development team spend to rectify the issue.
That total is the cost of downtime. It might not be as expensive as lost records, but it’s not going to do your business’s bottom line any favors either.
Cause of Data Breaches
Unsurprisingly, the majority of data breaches (47%) are caused by malicious entities.
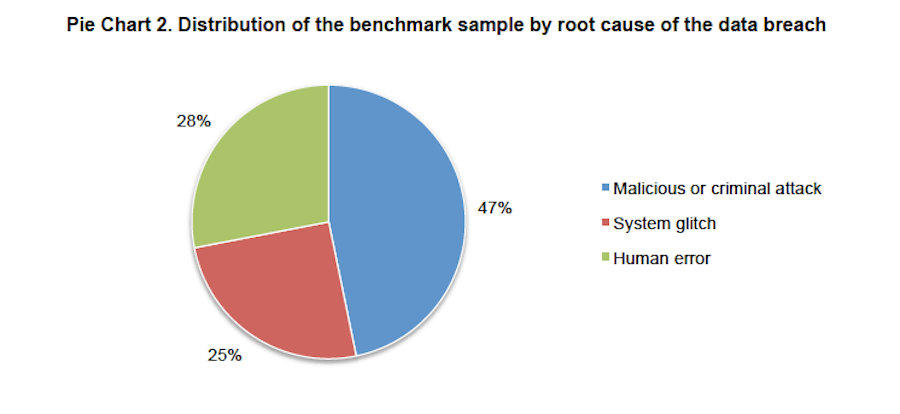
The other two causes of data breaches come from human error (28%) and system glitches (25%).
You can also see how much malicious attacks cost per capita when compared to system glitches and human error. The difference isn’t too significant, but it’s enough to make you want to fend off hackers as much as possible.
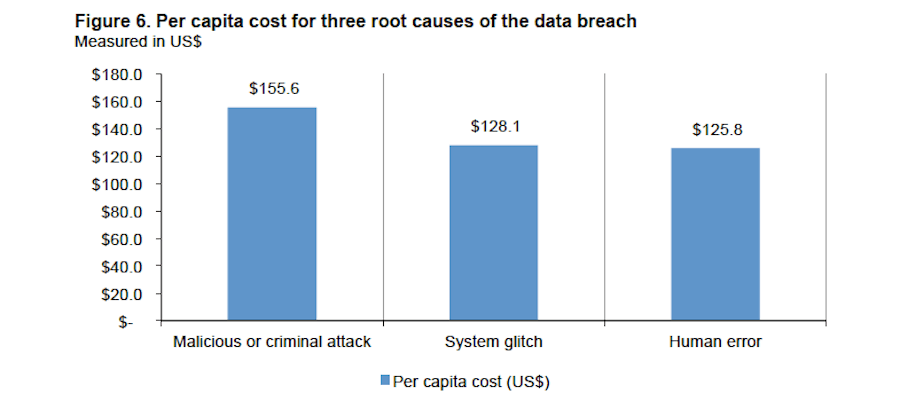
So, again, it’s important to be mindful of security risks that exist outside your WordPress site, but to also understand the dangers that exist within your own systems and teams. Disaster really can come from anywhere.
Other Factors that Contribute to Disaster-Related Costs
The total average cost of a data breach is quite frightening, isn’t it? But where exactly do those numbers come from? Is it how much money a company pays to customers to compensate for damages? Is it how much is spent on damage control for the brand? Actually, you might be surprised to learn where these costs come from.
1. Loss of Customers
This is what’s known as churn — the loss of customers and revenue.
As you can imagine, customers aren’t going to react well after they discover that any sort of disaster put their data at risk. The same goes for visitors who encounter a broken website, a hacked website, or one that’s down altogether. Disrupt their experience or put them in harm’s way and it could cost you a lot of customers that you’re now forced to spend money recouping in the following year.
2. Time to Identify and Contain the Problem
On average, it takes businesses 191 days to identify a security breach and an additional 66 days to contain it.
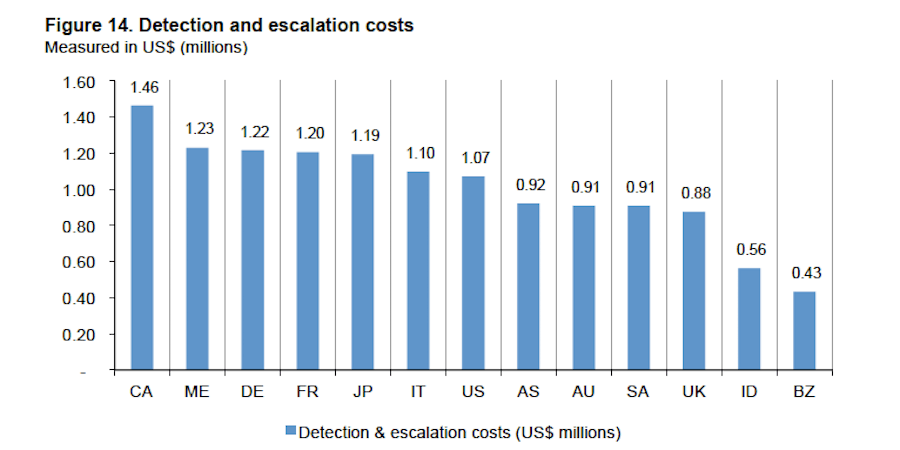
As you might imagine, when it takes nearly two-thirds of a year to do something about a breach of your records, the severity and depth of the problem is only going to worsen. The costs above reflect how expensive detection and escalation of breaches are to organizations every year.
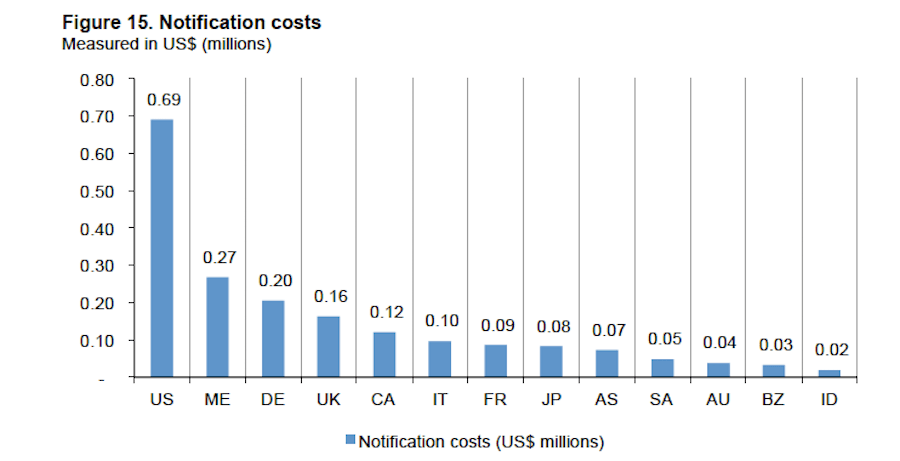
3. Notifications to the Public
Not only will a breach hurt your company’s reputation, but it’s going to cost you to handle the notifications and customer support surrounding it.
4. Post-Breach Activities
These are the activities you do after a breach has been detected and you’ve notified customers.
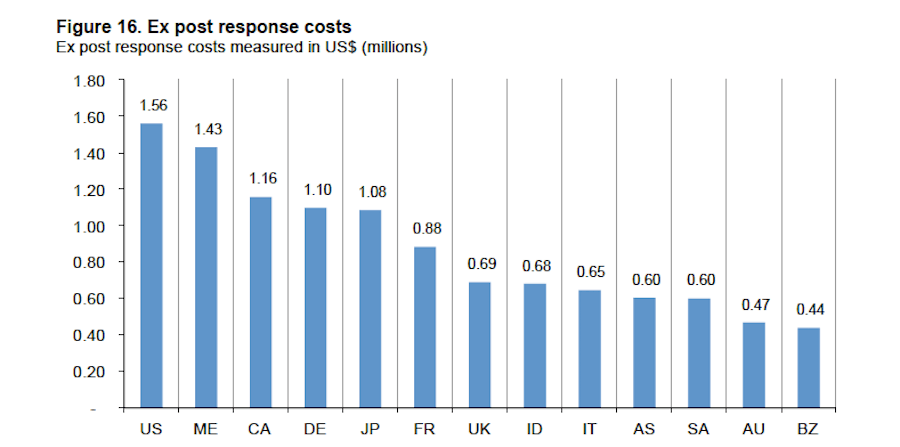
This includes things like:
- Help desk
- Inbound customer support communications
- Investigation into the cause of a breach
- Remediation work
- Hiring legal representation
- Offering product discounts and refunds
Basically, anything you do to clean up after the fact–including trying to salvage your customer relationships–falls into this category.
5. Other Factors That Influence Cost
The chart below breaks down some other factors that could positively or negatively affect the total costs of a breach.
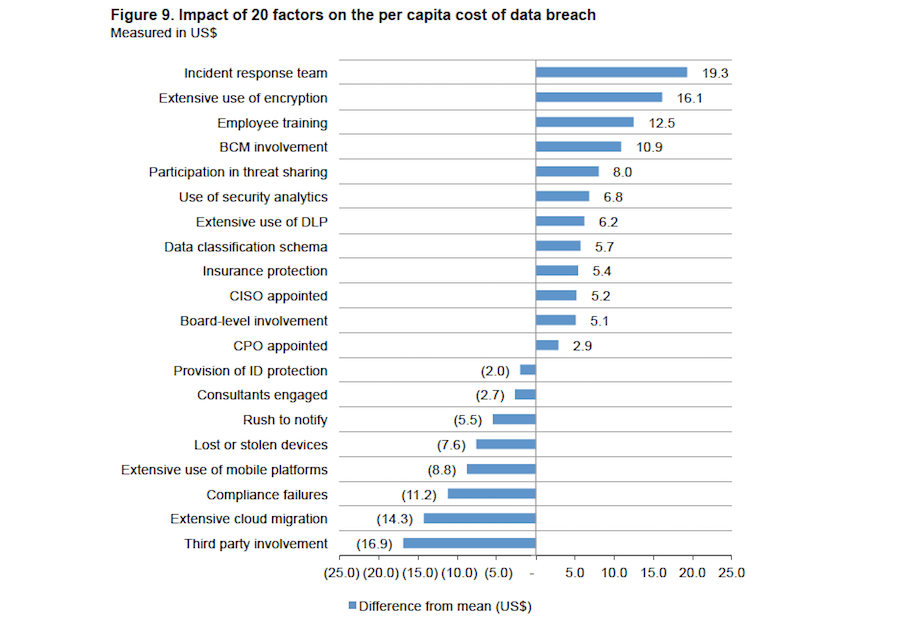
The things that could increase costs:
- Identity protection services
- Hiring of a consultant
- Mismanagement of notifications
- Extensive use of mobile systems to manage data
- Failure to follow compliance regulations (like GDPR)
- Third-party involvement
The things that could decrease costs (that have to be done before a disaster arises):
- Employing an incident response team
- Utilizing extensive encryption in your systems
- Implementation of an employee security training program
- Installing and monitoring security analytics
- Protecting your business assets with insurance
As you can see, a lot of this goes beyond the basics of what you think about when it comes to securing a WordPress website. That’s not to say that what you’ve been doing up until now isn’t right. It’s more that, if your company stands to lose a lot from a data security breach or any serious amount of downtime, there’s much more you should do to prevent, detect, and remedy the situation.
Your WordPress Disaster Recovery Plan: A Checklist
No matter how serious of a disaster your business is faced with, it can’t afford the consequences. Even if no sensitive information is compromised or leaked, there are other costs to contend with that add up.
Here’s what you can do about it:
Don’t panic. Disaster will happen at some point, so there’s no sense in worrying endlessly about the risk. But don’t completely ignore the possibility either. Instead, turn to your disaster recovery plan. This checklist includes all the steps you should take before, during, and after a disaster as you aim to recover from it.
Conduct a risk assessment.
Are there any gaps in security? Has your site been attacked within the last two years (which increases the chances of recurring attacks)? Is your industry at high-risk for attack? These kinds of questions will help you determine the likelihood of an attack and, consequently, focus on your weak spots.
Conduct a business impact analysis.
If your site were to go down, how much would it reasonably cost your business to bring it back up? If data were to be compromised, do you know how much would it cost to not only recover the website, but to pay for damages caused by the lost data? Can your business handle these costs? And how much time could your business stand to be without a website before you’re forced to close up shop permanently?
Figure out this threshold and plan the rest accordingly.
Define possible disasters.
Business disasters, in general, come in a broad list of forms. Website disasters, however, typically fall into one of a small handful of categories:
- Coding error
- Software conflict
- Malicious coding
- Malware, ransomware, spam, or other content infection
- DDoS attack
- Organic surge in traffic
- Natural disaster (server-side)
Lay down a strict security protocol.
A lapse in security is just one reason for disasters, but it’s a big one, so it deserves its own category. If you haven’t done so already, lay down a strict security protocol both inside and outside your WordPress site.
Create stricter access rules.
If you aren’t already, be very careful in choosing who receives full access to your WordPress site. By establishing more granular levels of access that keep users relegated to only the most relevant parts of WordPress, you can prevent the chance of user error from affecting your site.
Schedule backups.
One of the key elements in quickly restoring a damaged WordPress website is the backup. By creating and storing backups of your website on a separate cloud-based platform, you can effectively recover your online business in minutes. Not hours or even days. Make sure you have these scheduled to occur frequently (at least once a week).
Select monitoring methods.
It’s not sufficient to install a security plugin and call it a day. You need to monitor your website for all kinds of disasters, which means employing tools like uptime monitoring, malicious threat detection, security analytics, database change alerts, and so on. Automate these monitoring methods and set your tools to notify you on a daily basis of any issues. Serious issues detected should be delivered to your inbox in real time.
Define the recovery process.
The steps you take during a website recovery will, of course, be dependent on what sort of disaster you face. Cover all your bases and create robust documentation that lists out every step that needs to be taken, and by whom, in order to restore your website from a server outage, an injection of malware, a total site takedown, etc. You must be prepared for every scenario imaginable.
Start with your list of possible disasters and develop a custom response for each.
Designate a disaster response team.
You can’t just leave it up to machines to monitor and manage disaster threats. If your organization is large enough where the loss of data or a serious bout of downtime could cost you tens or hundreds of thousands of dollars (or, gulp, millions), you can’t afford to be without a disaster response team. They will be responsible for watching over your website and responding immediately after a threat is detected.
Train everyone else.
Employees as well as any third-party contributors or partners should be well-trained in disaster recovery and preparedness. This means educating them on security best practices as well as teaching them to spot the signs that something is wrong.
Create a list of contacts to repair the damage.
This is something that comes in handy for a traditional disaster recovery plan as the loss of equipment or workspace can disrupt one’s ability to communicate. That said, having a list of contacts for your WordPress site is important as well. In this case, your list will include individuals like:
- Your web hosting company’s support number or live chat link.
- Your incident response team.
- All the administrators of your website.
- The owner of the website (if it’s not your own).
- Employees who may have to deal with the cleanup or response.
- Your company’s legal team and other disaster recovery advisors.
They should be informed immediately so as to reduce the amount of time a disaster remains unchecked.
You should also have your business’s financial institution and credit reporting bureau on speed-dial. If your business’s financial data should get hacked, you’re going to want to save your assets as soon as possible.
Create a list of contacts to notify about the damage.
You should have your contact lists stored somewhere outside of WordPress:
- Clients
- Prospects
- Newsletter contacts
- Warm leads
- Cold leads
- Business partners
- Employees
Anyone who could potentially be affected by a data breach from the website should be notified. However, keep in mind that you shouldn’t respond in haste. Get all the details, assess how widespread the damage is, and take time to craft the appropriate response. You should have a support team immediately ready to step in and handle any backlash, too.
Test your preparedness.
At least once a year, schedule a preparedness test for your WordPress website. This should help you determine how prepared your site is to handle a disaster. You can do this by:
- Stress-testing your server.
- Attempting to log into the admin with the wrong credentials repeatedly.
- Digging into the backend of the site for revealing details that help others gain access.
- Incorrectly editing the code in the database.
- Submitting a spam comment to a blog post.
Think about where the most common threats come from and find a way to replicate them on your site. Of course, to keep your site safe from any damage you could do during the test, create a duplicate of it in a staging or local testing environment. Then, test your preparedness from there.
Switch hosts.
This step is optional, but it’s one I’m going to suggest you strongly consider now as it could improve your chances to prevent and be prepared for disaster in the future.
Take, for instance, how Pagely’s customers avoided disaster in early 2017. There was a vulnerability introduced to all WordPress sites by the REST API. However, Pagely took measures to patch its own servers with a Web Application Firewall in order to keep its customers safe.
If your web hosting company doesn’t prioritize security or provide assistance in the case of a disaster, then it’s time to look elsewhere. You need a partner who wants to see your website and its customers kept safe.
Wrap-Up
Preparing for disaster requires a lot of foresight and planning. If you want to decrease the likelihood of a disaster reaching your WordPress website, or, at the very least, reduce the costs to you and your business as a result of one, you must be prepared with a disaster recovery plan.
Remember: don’t just focus on the post-disaster recovery piece of it. The more you can prepare ahead of time, the more you can do to actively prevent disaster, and the closer of an eye you can keep on everything, the more quickly and positively you can resurface after it.
Of course, all of this requires a lot of time and resources to do it right. If you’re looking for assistance, Pagely’s managed WordPress hosting is a valuable resource for security, monitoring, and support.
